Showing 1 to 15 of 2075 results
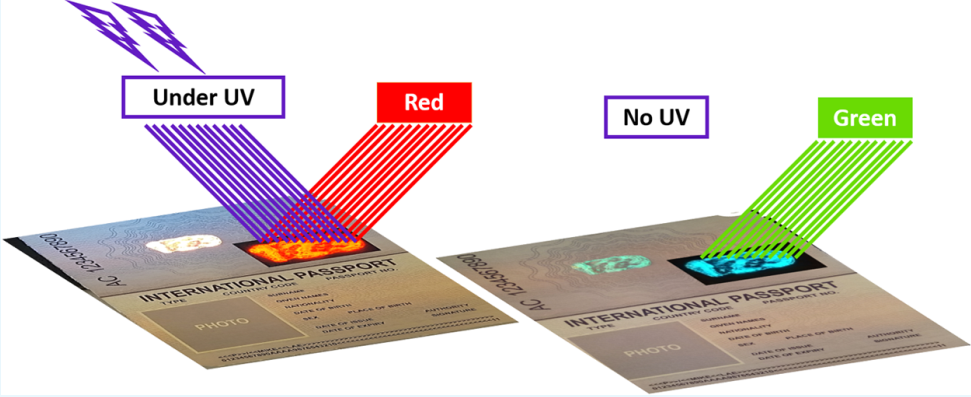
Ink for Anti-Counterfeiting security applications
Patents for licensing Mohammed VI Polytechnic University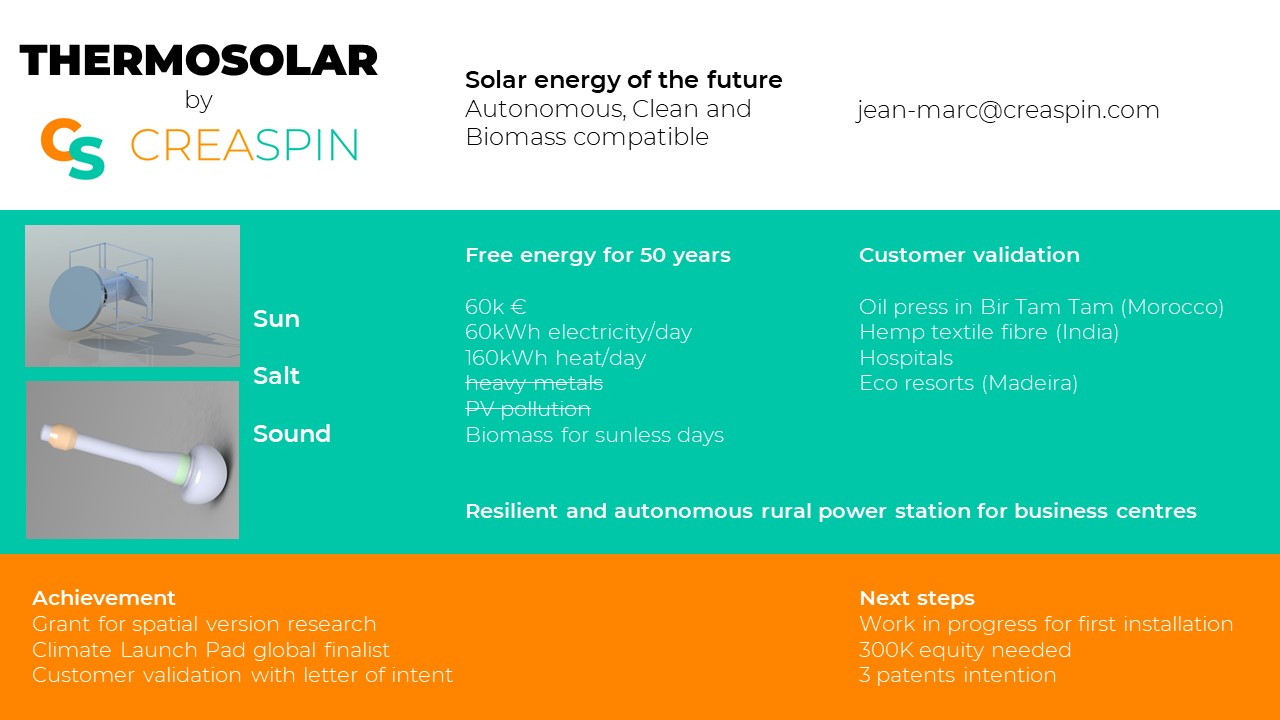

Thermosolar cogeneration power station
Investment Opportunities in Startups and Spinoffs Creaspin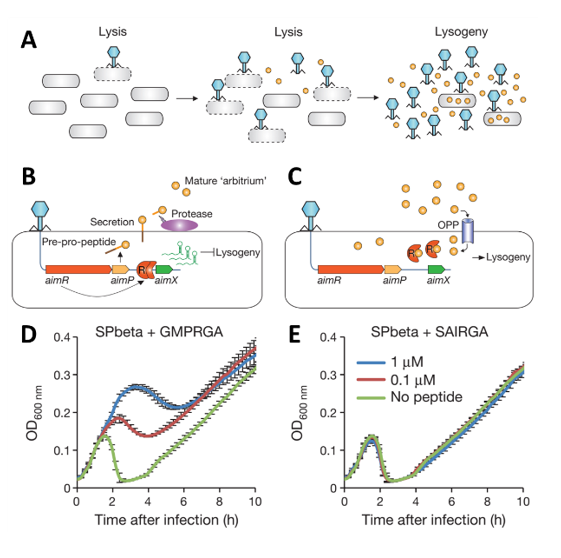

A Novel Synthetic Biology Platform for Controlling Gene Expression
Patents for licensing Yeda

Green Tech Innovation Centre
Research Services and Capabilities Luxembourg Institute of Science and Technology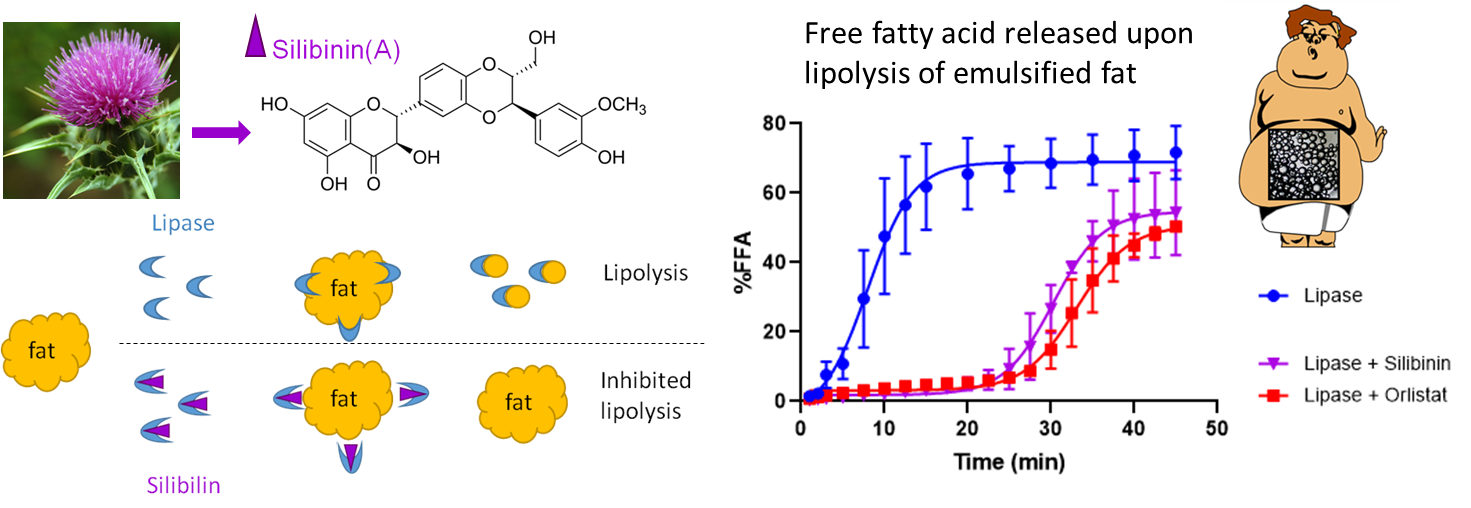

Compound for the treatment of obesity and hyperlipidemia
Patents for licensing Universidad de Granada

Andrographolide derivatives for its use as treatment for inflammatory diseases
Patents for licensing CSIC - Consejo Superior de Investigaciones Científicas

N4 -acyl-2-deoxycytidine-5-triphosphates for the enzymatic synthesis of modified DNA
Patents for licensing Vilnius University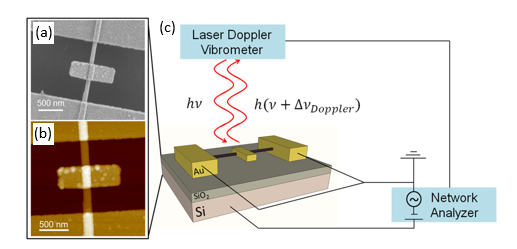

Inertial NEMS for Nanosensor Applications Based on Inorganic Nanotubes
Patents for licensing Yeda

Novel Antimicrobial Materials, with Broad-Spectrum Activity and Applicability in Medical and Non-Medical Applications
Innovative Products and Technologies MetalloBio Limited

TOP-seq: technology for high-resolution economical analysis of DNA epigenome
Patents for licensing Vilnius University

Biolimp-MPdry. Technology for biogas cleaning
Innovative Products and Technologies Energy & Waste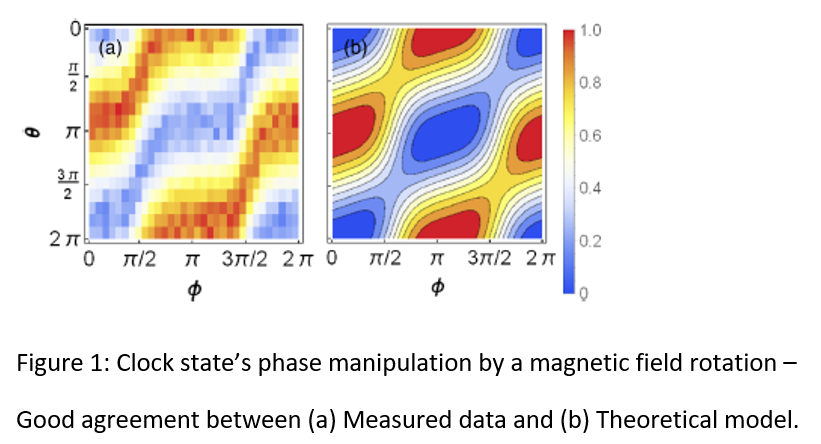

Atomic Magnetometer with Increased Coherence Time for Improved Magnetic Fields
Patents for licensing Yeda

Matrix metalloproteinase-2 Targeted Library
Innovative Products and Technologies Otava Research Institute

Histone Deacetylases (HDAC) Targeted Libraries. Screening compounds for epigenetic drug discovery.
Innovative Products and Technologies Otava Research Institute